In the world of cybersecurity, data breaches are the vampires of the digital realm. They lurk in the shadows, waiting to sink their teeth into your most personal information, leaving you exposed and vulnerable. Just as Halloween is a time for tales of the supernatural, it’s also an opportunity to shed light on the chilling consequences of data breaches and the ways your personal information can come back to bite you.
The Dark Allure of Personal Data
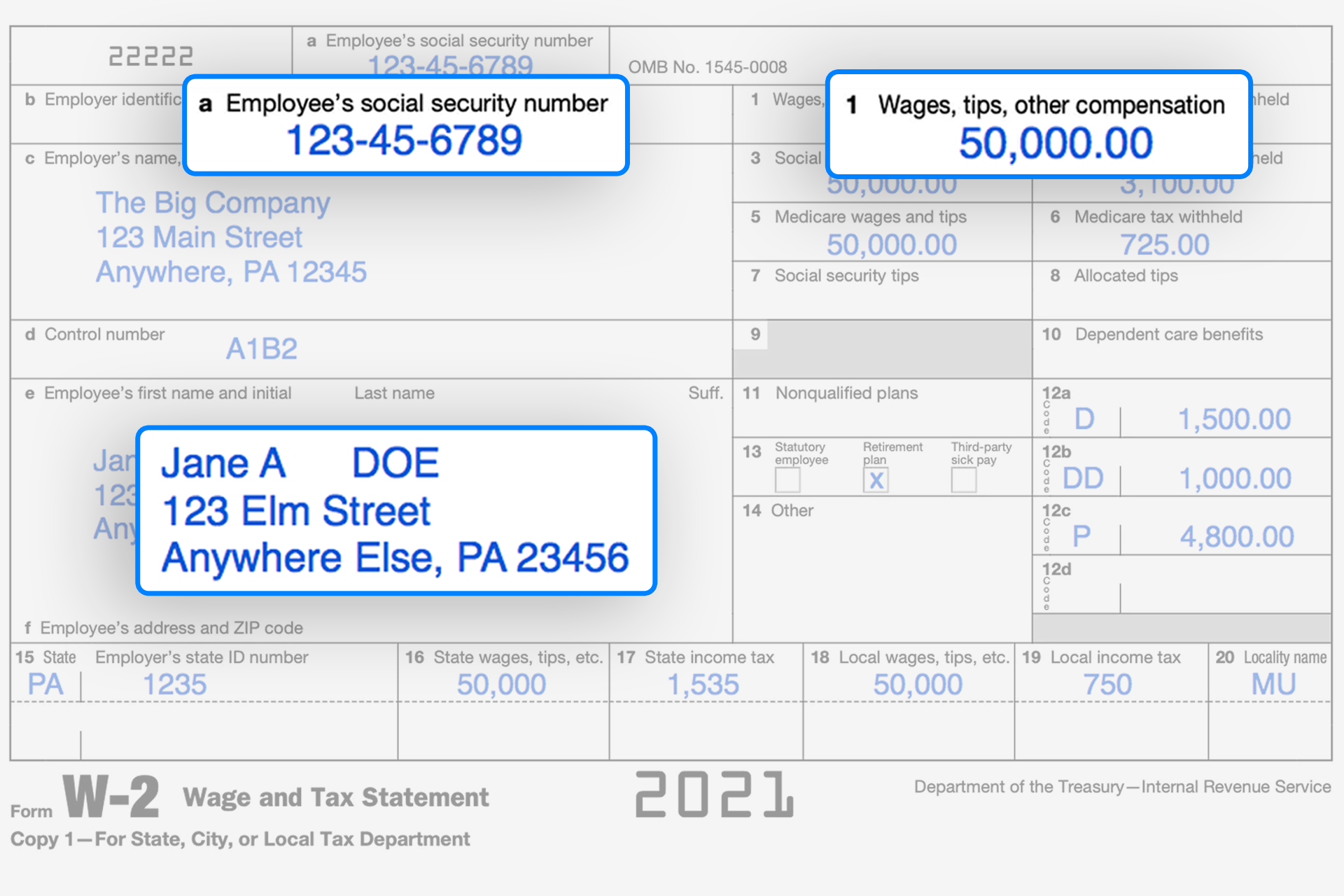
Hackers come for your personal data, like Dracula for blood. Your name, email, phone number, and even more sensitive information like financial details or healthcare records are valuable currency on the dark web. But what are the nefarious uses of this data?
Identity Theft: The most obvious danger is identity theft. Hackers can use your data to impersonate you, open accounts in your name, and commit financial fraud.
Stalking and Harassment: In the digital realm, hackers can exploit personal information for nefarious purposes such as stalking and harassment.
Ransomware Attacks: Cybercriminals may use your data to demand a ransom, threatening to expose or delete your sensitive information.
Hijacked Accounts: Your personal information can be leveraged to take over your online accounts, causing significant inconvenience and potential financial loss.
The Haunting Consequences of Data Breaches of Your Personal Information
Data breaches, much like a vampire’s bite, can leave lasting scars. They can result in severe financial, emotional, and even physical consequences:
Financial Loss: Stolen data can lead to financial ruin, as criminals siphon money from bank accounts, make unauthorized purchases, or commit fraud in your name.
Emotional Distress: Dealing with the aftermath of a data breach can be emotionally taxing. The violation of privacy and the fear of potential consequences can affect mental well-being.
Reputation Damage: Once your personal information is exposed, it’s challenging to regain your online reputation. Your data can be misused to tarnish your name and image.
Legal Complications: Data breaches can lead to legal issues, as victims seek compensation or companies face fines for failing to protect their customers’ information.
Defend Against Digital Vampires with DropSecure
To keep your personal information safe from the fangs of digital vampires, consider a reliable, secure file-sharing platform like DropSecure. Our encrypted file-sharing and storage solution fortifies your sensitive data, ensuring it remains hidden from prying eyes..
Here’s how DropSecure can help you:
End-to-End Encryption: Our end-to-end encryption is enabled using randomly generated AES 256-bit symmetric keys on your computer keeps your data safe, ensuring that only you and your intended recipient can access it.
Secure File Sharing: You can share files without fear, as DropSecure provides password-protected links and the ability to revoke access, just like a silver bullet for data security.
Monitoring and Control: Keep a vigilant eye on your shared files, ensuring that no unauthorized access occurs. Stay in control and monitor your communications. DropSecure offers activity tracking to give insights into who accesses your data and when.
Compliance Requirements: We meet global standards for data privacy and security. Your compliance needs are our priority, and we ensure that DropSecure aligns with regulations like GDPR and HIPAA, allowing organizations to work on sensitive data while maintaining compliance with data protection regulations.
This Halloween, as you embrace the thrill of spooky tales, remember that the chilling consequences of data breaches are all too real. Safeguard your personal information and protect yourself from the bite of digital vampires with endpoint security practices and a reliable tool like DropSecure.
Let’s fight off the digital darkness together and ensure that your data remains securely in your control, shielded from the vampires of the internet.